Bluetooth and WiFi are some of the most common connections between phones, smartwatches, TVs, computers, and many other devices. Both of them are much more developed and secure than ever before, but there’s no denying the potential risks involved with public connections. So, you might be wondering which option is more reliable and safe than the other.
When it comes to Bluetooth vs. WiFi, Bluetooth is typically more secure because it connects one device to another in a short-range. WiFi is quite safe, but it’s easier to hack because it has a broader range and can be accessed by nearby people. Leave your Bluetooth off when it’s not in use, though.
In this post, we’ll discuss potential security risks involved with using Bluetooth and WiFi. We’ll also talk about safety features, which one is more reliable than the other, and whether or not it’s okay to always leave them on.

Is Bluetooth More Secure Than WiFi?
Bluetooth and WiFi connections are typically equally secure when it comes to connection strength and reliability, but Bluetooth is often more secure from hackers. There are far fewer ways for people to hack into a Bluetooth device, especially since they have to be quite close to access the connection.
Here’s what you should know about why Bluetooth is usually more secure than WiFi:
- Bluetooth connections are shorter and always alert you when someone signs in. As Mozilla explains, your Bluetooth device doesn’t stretch nearly as far as WiFi connections can go. Additionally, Bluetooth connections follow the device rather than staying in one spot like a stationary router.
- WiFi connections can be protected by passwords, but some of them are open to the public. If you use a public WiFi connection, you’re putting your device at risk for all sorts of issues. Unfortunately, there are thousands of WiFi security problems every year. In fact, more people lose their data through WiFi than Bluetooth ever has.
- WiFi isn’t as foolproof, so hackers can steal sensitive data. Many weak WiFi connections are quite easy to break into, even if someone’s not an expert hacker. All you need to do is access the connected devices to find someone’s name, phone number, address, and other personal information.
- People can almost track your exact location if they hack your Bluetooth device. While Bluetooth is mostly safe, the limited proximity means people can find your location quite quickly. They can stay within range to find out who has the primary host device within about 50 feet of them.
- Bluetooth location services can send ads through your devices. Since Bluetooth heavily depends on its location, local ad networks can send you all sorts of junk. While it’s not necessarily a security risk, it’s quite annoying and avoidable by turning off your Bluetooth device when it’s not being used.
As you can see, WiFi isn’t as secure as Bluetooth. However, neither of them is resistant to every hacker or digital attack. In the next two sections, we’ll dive into the risks and potential issues associated with using Bluetooth and WiFi to find out how you can keep your data and location safe from harm.

Is Having Bluetooth On a Security Risk?
Having Bluetooth on is a security risk if you’re in a public area or apartment complex. Anyone near your Bluetooth device can try to access the network. If you don’t have a password or two-step authentication set up, they can jump into the connection and play songs, download anything, and more.
So, is Bluetooth always a risk to use? Review these four must-know factors:
- Using Bluetooth isn’t a problem, but leaving it open and unused can invite hackers and unwanted visitors. Many people make the mistake of leaving their Bluetooth on because they don’t want to click it whenever they want to use it next. However, they’re leaving their connection open to anyone near them.
- Bluetooth connections consume data and battery life, even if it’s not from your device. If someone connects to your device, your batteries will drain. Even if nothing is connected, the Bluetooth connection searches for devices and leeches the battery life while exposing your phone to ads.
- You can always monitor who joins your Bluetooth connection. Although you might’ve accidentally left the Bluetooth icon activated, you can always check who’s using it. Go to your device’s Bluetooth settings and check for all connected devices. You can click them and kick them out if you don’t know who or what they are.
- Weak devices leak personal information via Bluetooth. Keeping your smartphone, TV, and computer updated will prevent security risks through Bluetooth connections. Almost all software updates contain minor security improvements to make it harder for hackers to steal your data, so keep up with them!
Leaving your Bluetooth activated isn’t the best idea, but it’s also not the end of the world. The biggest issue you’ll likely face is a quick-draining battery. Other than that, you’d have to be in a public location to be at risk. Remember, Bluetooth connections are quite short.

What Are the Risks of Using WiFi?
The risks of using WiFi include potential hackers stealing your data, people finding your location, or malware downloading onto your device. Furthermore, using public WiFi puts your device at risk for middle-man issues, which include people using your device to download illegal content onto their device.
Keep these four issues in mind when using WiFi:
- Public WiFi is accessible by anyone, including hackers. According to Consumer Information, public WiFi lets hackers log into random websites using your login information. They can check your bank account numbers, subscriptions, and more, leaving your financial and personal life exposed.
- WiFi often provides more power to the host, which means they can control your device and personal information. If you connect to any WiFi connection that you don’t own, the primary provider can kick you off whenever they feel like it. They can also check what websites you’ve accessed.
- Some WiFi connections drop malware onto your device. While this issue is usually associated with sketchy public WiFi connections, any WiFi connection has the potential to download malware onto your device. Always run malware and virus scans after using WiFi that you don’t own, especially if it’s open to the public without a password.
- Secured, password-protected WiFi isn’t very dangerous at all. While people often stress out about using WiFi, it’s actually much safer than it used to be. Secured WiFi is very safe, especially if you’re the owner or you know the primary host. Even so, these issues are increasingly rare since hackers can be tracked.
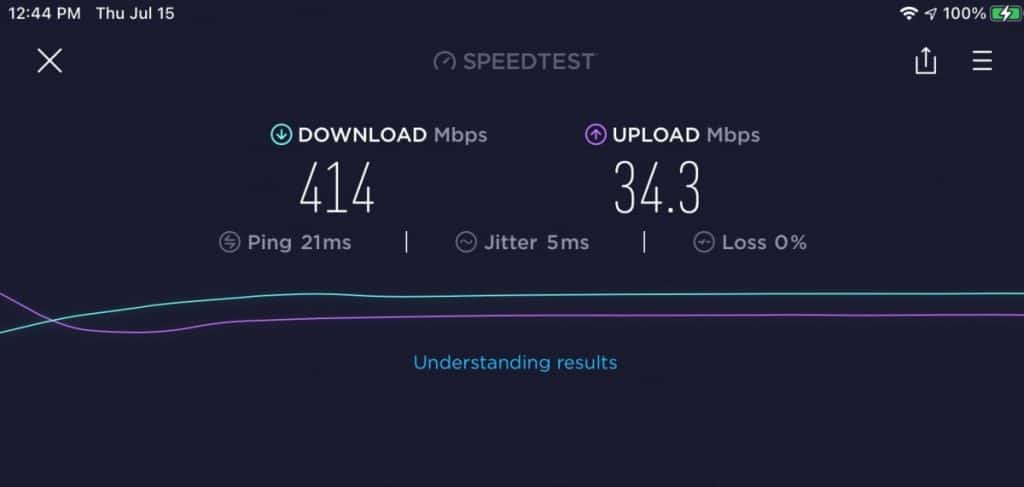
It’s better to be safe than sorry, so make sure you know everything about the WiFi network you’re trying to use. We suggest sticking to cellular data or a mobile hotspot if your only other option is public WiFi without a password. These connections provide more reliability and peace of mind.
Can My Bluetooth Be Hacked?
Make Use Of claims all Bluetooth devices can be hacked, ranging from smartphones to cars and more. You can protect your devices by leaving the Bluetooth connections off when you’re not using them or turn your device (or car) to non-discoverable in its Bluetooth settings. Either route will ensure people can’t locate or access the device via Bluetooth.
People can hack Bluetooth devices by sending encrypted messages, ads, malware, or attempting to steal your location details. Some hackers can take complete control of your device, but this is quite rare. All hacking attempts are ruined if you turn off your Bluetooth network since it’s required for them to maintain a connection to the device.
Is WiFi Easier to Hack Than Bluetooth?
WiFi is easier to hack than Bluetooth because it takes less effort to find someone’s location and private data over an unsecured public network. However, skilled hackers can get into most devices with Bluetooth or WiFi connections, so neither method is completely foolproof. Run malware scans to protect your device.
Keep an eye on your Bluetooth or WiFi-connected devices to look for anything suspicious. While companies are constantly making security improvements, hackers are right behind them, trying to figure out how to break the next barrier.
How to Know if Your WiFi is Secure
Knowing your WiFi is secure will let you browse the internet and online apps without risking your personal information. If you want to know if your WiFi network is protected, follow the step-by-step process below.
- Check your WiFi log (if you’re the owner). Download your service provider’s app (if they have one) or access their website. Log in to the app or site, then check through all of the connected devices. You can see when the most data was used, who accessed it, and more. This log should be a part of your weekly routine.
- Run virus scans weekly to prevent people and programs from adding malware. There are many virus software programs to protect your devices from all sorts of malware. Whether you’re using a smartphone, tablet, or computer, we highly suggest sweeping your WiFi-connected devices regularly.
- Set alerts on your phone to know when anyone connects to the WiFi. A quick notification can let you know if a stranger accesses your WiFi network. Click the listing and boot them off. You can also choose to permanently block them, preventing them from trying to enter another password.
- Restart your router occasionally to log every device off of it. Restarting your router will log everybody off, but it’ll also loosen the cobwebs and bring your router back to its normal speed. Some routers have software updates, so make sure yours is up to the current update to prevent security risks.
- Contact your WiFi provider if you experience random outages, lagging, or bandwidth issues. While we’ve all experienced normal lagging, it shouldn’t be a constant issue. Some hackers can hide their presence on your WiFi network, so contact your service provider and check who’s online.
Should You Disable Bluetooth and WiFi if They’re Not Used?
You should disable Bluetooth and WiFi if they’re not being used to prevent people and malware from tracking your information or location. While it’s quite unlikely that someone will pick up an open network on your device, it’s not impossible. It’s better to leave them off unless you’re using them.
- Disabling your Bluetooth prevents hackers from finding your data. For example, when you activate Bluetooth on your smartphone, anyone near it can try to access it. Turning off the icon when it’s not being used immediately protects your phone from every potential Bluetooth issue.
- Your device will only connect to WiFi if you choose to ‘remember’ the connection. If you don’t want to accidentally connect to a public WiFi source, don’t let it remember any of the connections. You can turn this off in our phone’s settings > connections menu or choose to forget it before logging off.
- Always turn off Bluetooth when it’s not being used to stop your battery from draining. Bluetooth connections are known to drain a device’s battery life. It’s always searching for a nearby device, but turning it off stops it in its tracks. You’ll enjoy much more battery life from your device.
- Run a fresh reset every few weeks on your router to clear unknown connections. Turn the router off and on every so often, and you’ll be impressed by how quickly it loads and connects your devices. Routers aren’t designed to stay on at all times; Give it a quick rest to keep it in good condition.
Disabling WiFi and Bluetooth connections when you’re not using them is best for peace of mind. Someone can’t hack your device via either network if you don’t have them activated.

Conclusion
Now that you know all of the potential risks involved with using WiFi and Bluetooth, you can decide which you prefer more. Truthfully, both connections can be quite safe since they’re protected by passwords. Some connection services let you kick people off of the connection or place a two-way authentication as an additional barrier.